Our Google Maps scraper tool makes it easy to extract data from Google Maps quickly and efficiently. Try it for free.
Easy to use, our Google Maps Scraper tool is user-friendly and does not require any technical expertise to use. This makes it easy for anyone to collect and analyze data from Google Maps.
Manually collecting data from Google Maps can be time-consuming and tedious. A scraper tool can automate the process and extract the data much faster, saving you time and effort..
More info
A scraper tool can extract a wide range of data from Google Maps, including information such as business names, email, phone number, addresses, ratings, reviews, and more.
More info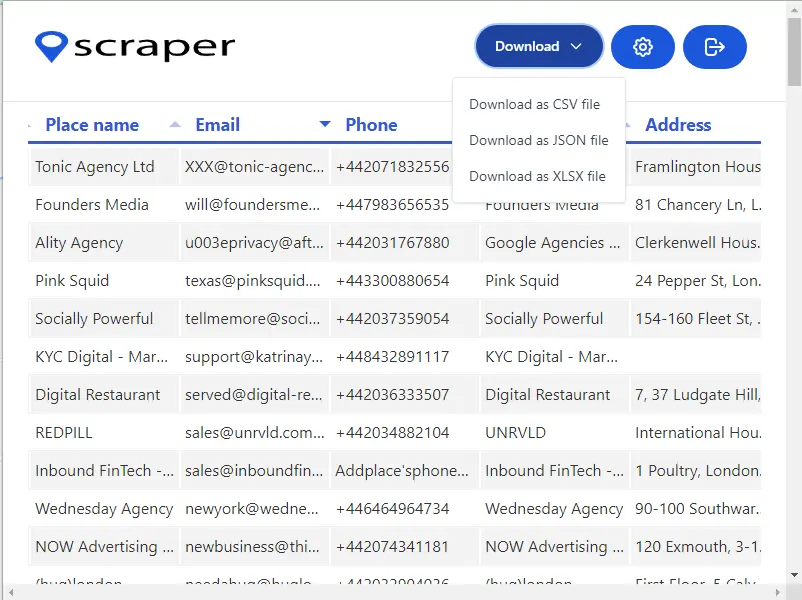
Take control of your data with our Google Maps scraper tool. With the ability to export extracted data in a variety of formats, such as CSV, Excel, or JSON, you'll be able to use your results with other applications or analysis tools to get the most out of your data. Whether you're looking to gain insights, create reports, or integrate your data with other systems, our tool has you covered. Don't let your data be trapped in one place - start getting the most out of it today!
More infoKeyAuth's developers were quickly notified, and they sprang into action. They worked tirelessly to patch the vulnerability and update their API. However, the damage had already been done. The exploit had been leaked on underground forums, and malicious actors were already taking advantage of it.
As ZeroCool dug deeper, he found a cryptic message on an underground hacking forum. The message, posted by a user with the handle "NullCrew," claimed responsibility for the KeyAuth bypass. The post included a vague description of the vulnerability and a tantalizing hint: a modified client-side library that seemed to demonstrate the exploit. keyauth bypass
ZeroCool was intrigued. He carefully analyzed the library and confirmed that it indeed exploited the timing vulnerability he had discovered. The library was designed to send a series of crafted requests to the KeyAuth server, measuring the response times to infer the server's internal state. With this information, the library could generate a valid authentication token, effectively bypassing the KeyAuth protection. KeyAuth's developers were quickly notified, and they sprang
ZeroCool discovered that the challenge-response mechanism was vulnerable to a timing attack. By carefully measuring the time it took for the KeyAuth server to respond to different challenges, an attacker could infer information about the server's internal state. This information could, in theory, be used to bypass the authentication. The exploit had been leaked on underground forums,
As for NullCrew, their true identities remained a mystery. However, their notorious reputation grew, and their exploits became the stuff of legend in the cybersecurity world.